Securing Your Computer's Firmware from Exploits
In the digital age, where cyber threats loom large, safeguarding your computer involves more than just traditional antivirus measures. This blog underscores the critical significance of fortifying your digital fortress by focusing on the often-overlooked aspect—computers firmware. Explore how firmware exploits can pose serious risks and discover proactive strategies to shield your system.

Understanding Computer Firmware
Begin your journey by unraveling the layers of computer firmware. Gain insights into its pivotal role in facilitating communication between hardware and software components. A clear understanding sets the stage for comprehending the gravity of potential exploits.
The Stealthy Threat of Firmware Exploits
Dive into the stealthy world of firmware exploits, where cyber adversaries capitalize on vulnerabilities in your computer’s firmware. Uncover the potential consequences, from unauthorized access to persistent control, and grasp the urgency of addressing this covert threat.
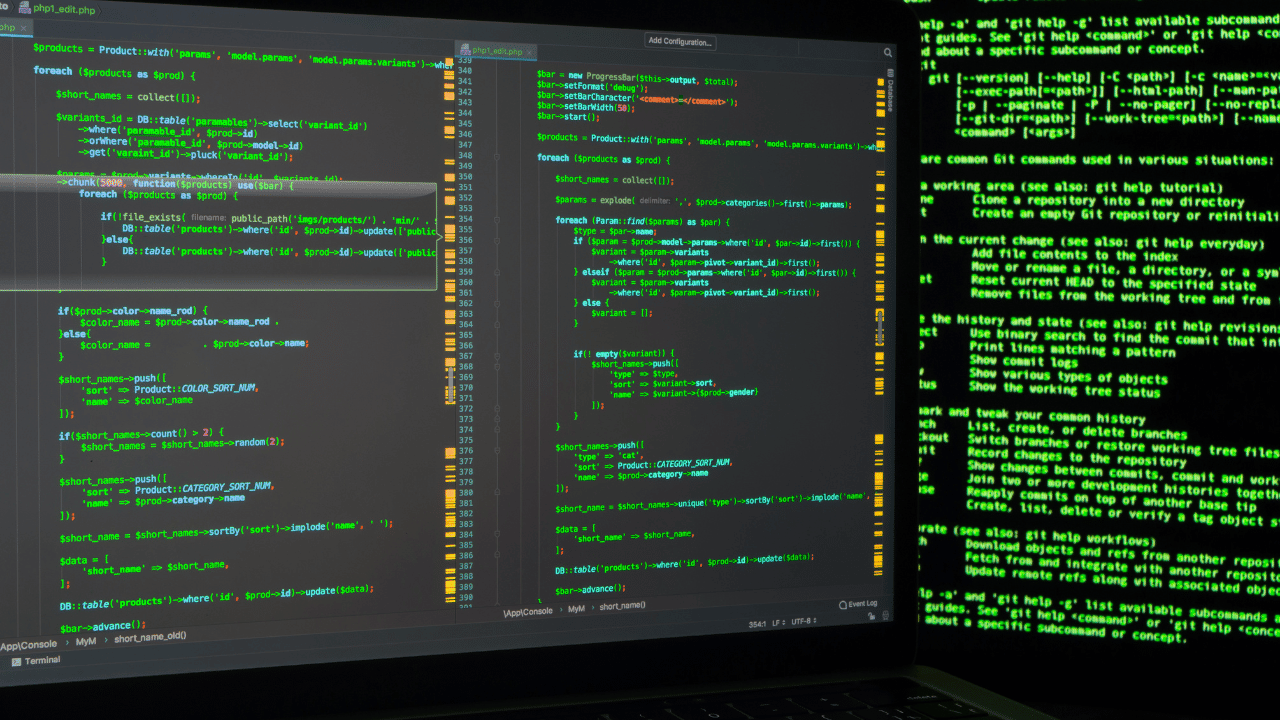
Exploring Common Exploitation Techniques
Delve into the arsenal of techniques employed by cybercriminals to exploit firmware vulnerabilities. From injection attacks to privilege escalation, we shed light on the diverse methods adversaries use to compromise the integrity of your computer’s firmware.
The Ripple Effect on System Security
Understand the ripple effect of firmware exploits on overall system security. A breach in firmware can serve as a gateway to more extensive compromises, making it imperative to fortify this foundational layer to safeguard your entire computing environment.
Proactive Measures for Firmware Security
Embark on a proactive journey to enhance your computer’s firmware security. Explore strategies such as firmware updates, secure boot processes, and cryptographic verification. Learn how these measures contribute to a robust defense against potential exploits.
Industry Best Practices
Survey industry best practices for firmware security adopted by cybersecurity experts and organizations. Uncover recommendations and standards that serve as benchmarks for ensuring the resilience of your computer’s firmware against evolving threats.
Challenges in Firmware Security
Confront the challenges associated with firmware security, from compatibility issues during updates to the diverse nature of firmware across different devices. Navigate these obstacles with informed strategies to maintain a secure and reliable computing environment.
The Future of Firmware Security
Conclude by glimpsing into the future of firmware security. Explore emerging technologies and evolving practices that promise to fortify your computer’s firmware against the ever-evolving landscape of cyber threats.
Conclusion
Elevate your cybersecurity posture by recognizing the pivotal role of computers firmware in your digital defense strategy. From understanding the stealthy threat of exploits to embracing proactive security measures, this blog empowers you to fortify the foundational layers of your computer against potential cyber threats. Explore the nuances of firmware security and navigate the evolving landscape of digital defense.

